Lesson 1
An Introduction to Your Nanodegree Program
Welcome! We're so glad you're here. Join us in learning a bit more about what to expect and ways to succeed.

Nanodegree Program
This program will equip students with the skills they need to advance in their security career and become an Ethical Hacker or Penetration Tester.
This program will equip students with the skills they need to advance in their security career and become an Ethical Hacker or Penetration Tester.
Advanced
2 months
Real-world Projects
Completion Certificate
Last Updated June 12, 2024
Skills you'll learn:
Prerequisites:
Course 1 • 45 minutes
Lesson 1
Welcome! We're so glad you're here. Join us in learning a bit more about what to expect and ways to succeed.
Lesson 2
You are starting a challenging but rewarding journey! Take 5 minutes to read how to get help with projects and content.
Course 2 • 4 weeks
The purpose of this course is to introduce students to the broad set of techniques and job responsibilities associated with the role of an Ethical Hacker. Ethical Hackers leverage their knowledge of business’ processes to evaluate risks while protecting core operations. The results of an Ethical Hacker’s efforts are improvements to business policies, procedures and standards of conduct on its computer systems.
Lesson 1
Meet the instructor, get an overview of the course and start learning about why Ethical Hacking is such an exciting field. Let's get started!
Lesson 2
Perform a vulnerability scan using automated tools, manage prioritization and response, and score the vulnerabilities you uncover
Lesson 3
Use test scopes to understand the context and objectives of an audit, gather information about our target, research vulnerabilities, execute exploits, and write effective reports on our findings
Lesson 4
Use OWASP WTG methodologies, create HTTP requests to access target systems and employ semi-automated and fully-automated tools in applications audits
Lesson 5
Explore the tactics malicious hackers use to manipulate people to take specific actions, conduct a phishing simulation, create and deploy malware and design an effective landing page
Lesson 6
Employ open-source intelligence techniques to uncover information leakage. Use Exploratory Link Analysis techniques to mine data, establish links between the data and analyze the links
Lesson 7 • Project
Use the skills you have developed in this course to manage a full-fledged security audit of a fictitious company called ExampleCorp
Course 3 • 4 weeks
The purpose of this course is to take a deep dive into the specific technique of penetration testing and how it can be used to perform a cybersecurity assessment on a specific system and conducted as a part of a specific penetration testing project within an organization to identify vulnerabilities, flaws and risks.
Lesson 1
Brief introduction and foundational knowledge around penetration testing and red teaming.
Lesson 2
In this lesson, we will dive into the first step of penetration testing which focusses on gathering information and data about the target, also known as Reconnaissance.
Lesson 3
In this lesson, we will use the information we obtained in reconnaissance to become informed and plan how to breach the target.
Lesson 4
In this lesson, we will now execute on the information we have from reconnaissance, scanning, and research and will now execute on the plan of how to gain access on the target.
Lesson 5
In this lesson, we will learn how to maintain the access that we just go on the target.
Lesson 6
In this lesson, we will learn how to stay under the radar of the target and not be noticed. And we will also organize all our thoughts in a final comprehensive report.
Lesson 7 • Project
This project will have you go through modern penetration tester and red teamer methodologies. You will create a documentation and testing efforts to generate a report in a timely fashion.
Course 4 • 10 minutes
Lesson 1
Congratulations on your graduation from this program! Please join us in celebrating your accomplishments.

Founder of PJ Pros
Paul Oyelakin is the founder of PJ Professional IT Services. He has experience in security compliance, penetration testing, and architecting network security solutions for business and government. He has an MBA, MS in Cybersecurity, and is a Certified Ethical Hacker & Information System Security Professional.

Chairman at Bansal X
Sagar Bansal is a consultant, speaker, and author in the information security industry. He helps large enterprises, governments and intelligence agencies reduce the cost of security by creating reliable and proactive security workflows.
Average Rating: 4.2 Stars
17 Reviews
Reema M.
January 31, 2023
Amazing
Francis H.
August 17, 2022
It has been much harder than I expected. Although it can be mentally draining at times, nothing good comes out of easiness. I just think that the fact that the program is 2-3 years old, it seems like the Kali linux version might be out of date and some of the tools used during the course might not play well with an outdated version of Kali and so forth. Overall, no major issues and I've learned a whole lot!
sven v.
February 7, 2022
great
Enrico Maria C.
November 3, 2021
This was one of the best online courses I ever attended! Congrats!
Komsan N.
October 20, 2021
This program cover all about the basics of ethical hacking. As a software developer is really useful to audit our software system. For example finding vulnerabilities, even introducing various tools to help the job done.
Combine technology training for employees with industry experts, mentors, and projects, for critical thinking that pushes innovation. Our proven upskilling system goes after success—relentlessly.
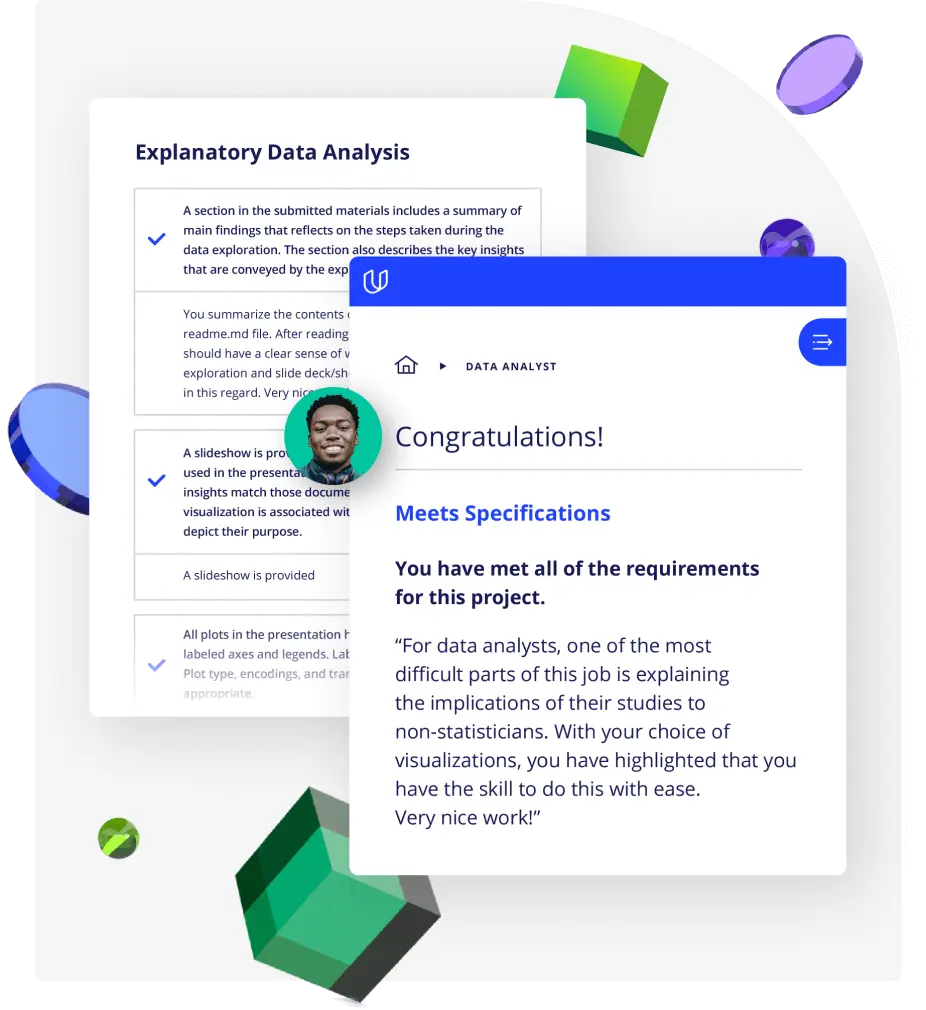
Demonstrate proficiency with practical projects
Projects are based on real-world scenarios and challenges, allowing you to apply the skills you learn to practical situations, while giving you real hands-on experience.
Gain proven experience
Retain knowledge longer
Apply new skills immediately
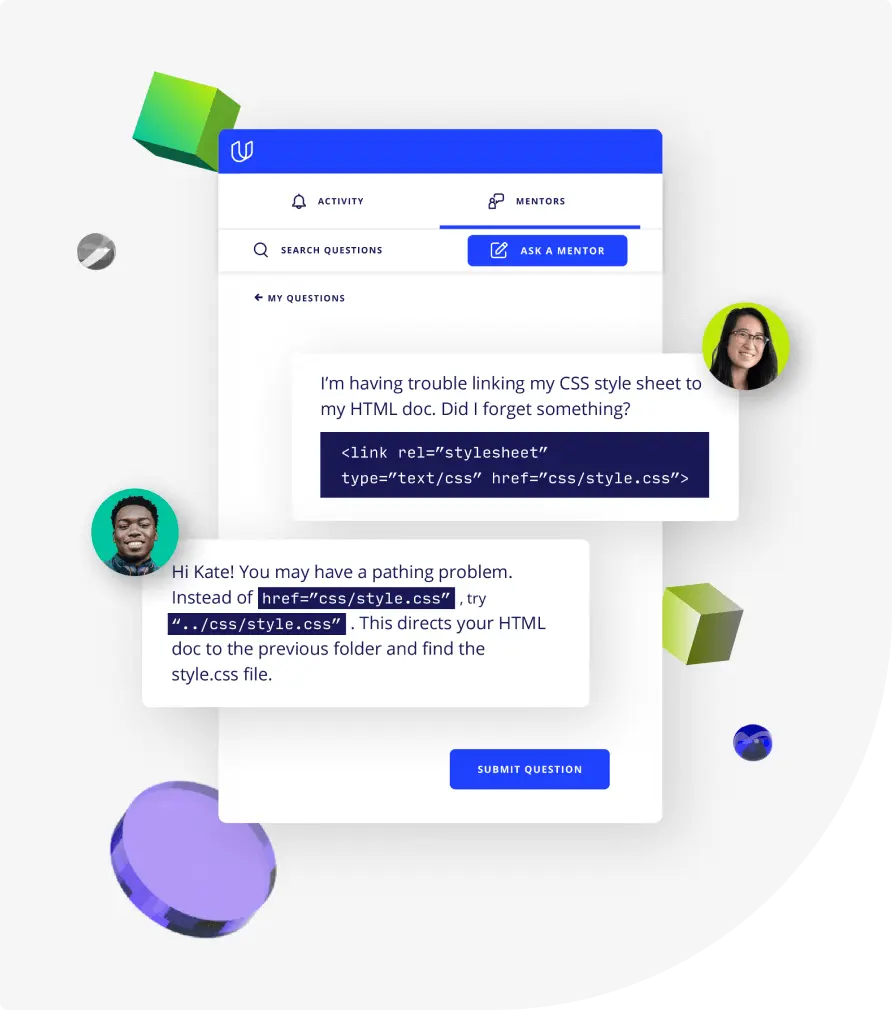
Top-tier services to ensure learner success
Reviewers provide timely and constructive feedback on your project submissions, highlighting areas of improvement and offering practical tips to enhance your work.
Get help from subject matter experts
Learn industry best practices
Gain valuable insights and improve your skills
Unlimited access to our top-rated courses
Real-world projects
Personalized project reviews
Program certificates
Proven career outcomes
Full Catalog Access
One subscription opens up this course and our entire catalog of projects and skills.
Average time to complete a Nanodegree program
4 weeks
, Advanced
(115)
3 months
, Beginner
(9)
4 months
, Intermediate
(32)
4 months
, Intermediate
(27)
4 months
, Intermediate
(6)
4 weeks
, Beginner
4 weeks
, Intermediate
4 weeks
, Intermediate
4 weeks
, Beginner
4 weeks
, Beginner
4 weeks
, Advanced
4 weeks
, Beginner
(47)
4 months
, Intermediate
(729)
3 months
, Intermediate
4 weeks
, Intermediate
(93)
2 months
, Intermediate

Ethical Hacker
4 weeks
, Advanced
(115)
3 months
, Beginner
(9)
4 months
, Intermediate
(32)
4 months
, Intermediate
(27)
4 months
, Intermediate
(6)
4 weeks
, Beginner
4 weeks
, Intermediate
4 weeks
, Intermediate
4 weeks
, Beginner
4 weeks
, Beginner
4 weeks
, Advanced
4 weeks
, Beginner
(47)
4 months
, Intermediate
(729)
3 months
, Intermediate
4 weeks
, Intermediate
(93)
2 months
, Intermediate