Lesson 1
An Introduction to Your Nanodegree Program
Welcome! We're so glad you're here. Join us in learning a bit more about what to expect and ways to succeed.

Nanodegree Program
The Enterprise Security Nanodegree program imparts foundational skills in security engineering for corporate environments. Covering network and data security, endpoint protection, and application security, you will learn to design robust defenses, manage data integrity, and comply with privacy regulations, which will enhance the security posture of any enterprise.
The Enterprise Security Nanodegree program imparts foundational skills in security engineering for corporate environments. Covering network and data security, endpoint protection, and application security, you will learn to design robust defenses, manage data integrity, and comply with privacy regulations, which will enhance the security posture of any enterprise.
Beginner
4 months
Real-world Projects
Completion Certificate
Last Updated June 18, 2024
Skills you'll learn:
Prerequisites:
Course 1 • 45 minutes
Lesson 1
Welcome! We're so glad you're here. Join us in learning a bit more about what to expect and ways to succeed.
Lesson 2
You are starting a challenging but rewarding journey! Take 5 minutes to read how to get help with projects and content.
Course 2 • 4 weeks
In this course, you'll learn how to: design a secure network architecture; build secure network architectures in Azure; set up continuous monitoring and alerts using a SIEM; and create a Zero Trust Model.
Lesson 1
In this introductory lesson, we'll give you a helpful overview of the course that will set you up for success!
Lesson 2
In this lesson we'll provide you an introduction to network security architecture for enterprise.
Lesson 3
In this lesson we are going to take all the concepts we learned from Network Security Architecture and use them to build our own secure enterprise network in Microsoft Azure.
Lesson 4
In this lesson we'll learn how to set up continuous monitoring for our enterprise network through the use of a SIEM.
Lesson 5
In this lesson we'll introduce you to a new school of thought in how enterprises should best secure their network - Zero Trust.
Lesson 6 • Project
In this project, you'll design a secure network architecture for a simulated business context, build that design in Azure, set up monitoring with a SIEM, and create a Zero Trust Model.
Course 3 • 4 weeks
In this course, you will learn about how to craft Enterprise level Endpoint security policies and hardening strategies.
Lesson 1
This is the welcome lesson to Enterprise Endpoint Security. Here you'll get a quick overview of what we'll cover in the course.
Lesson 2
In this lesson, you will learn how to develop a hardening strategy to ensure the security of endpoints across all enterprise-owned devices.
Lesson 3
In this lesson, you will build security policies that implement compliance requirements to secure enterprise devices and data using industry best practices.
Lesson 4
In this lesson, you will use best practices to create automated Cloud Endpoint Security procedures.
Lesson 5 • Project
This is the project lesson for this course. Here you will complete and submit your project for this course.
Course 4 • 4 weeks
Application security is a critical part of any enterprise security plan. We will be cover how to perform a threat assessment by doing threat modeling and pen testing. This course will teach mitigation and defensive strategies in an application software development lifecycle. The focus will be on covering how enterprises bake security into their lifecycle by shifting security left and the different ways they enhance their security posture across on-premise, cloud, containers, and APIs.
Lesson 1
This is the welcome lesson to Enterprise-Wide Application Security. Here you'll get a quick overview of what we'll cover in the course.
Lesson 2
Designing security architecture is the first phase, where you set the teams and architecture. You will learn about DevSecOps, SDLC, and security architecture in this lesson.
Lesson 3
In the threat hunting phase, you will proactively find security issues in the product. You will learn about threat modeling, identify vulnerabilities, vulnerability scanning, and pen test roadmap.
Lesson 4
In this lesson, you will scan containers, research container vulnerabilities, and mitigate container vulnerabilities, so that you can better handle the actual deployment and cloud infrastructure.
Lesson 5
API service is what the end-users will finally use. In this lesson, you will identify coding vulnerabilities, mitigate coding vulnerabilities, and learn about monitoring and analytics.
Lesson 6 • Project
In this project, you will become the lead security architect for a new startup’s web application and be tasked to identify vulnerabilities and creating a roadmap for mitigation.

Cybersecurity Architect, Head of Product Technology
Vamsee has wide-ranging security experience, in sectors such as defense and automotive. He studied electrical engineering, then focused on cybersecurity during graduate school at Carnegie Mellon. He enjoys working on latest technologies and high-impact solutions.

Founder & CEO, Cyber Pop-up
Dr. Christine Izuakor is the CEO of Cyber Pop-up, an on-demand cybersecurity platform powered by vetted cyber freelancers. She has over a decade of experience leading cybersecurity functions within Fortune 100 companies and has her PhD in Security Engineering.

Information Security Engineer
Jerry is a member of the Security Operations Center for the University of Alabama Birmingham, where he is the lead Threat Hunter and a member of the firewall team. Previously he was an Information Security Engineer for Hibbett Sporting Goods.

SECURITY ENGINEER
Milind Adari is a Security Engineer at The Associated Press and an Adjunct Instructor at Columbia University. He is responsible for protecting journalists all around the world from malicious threat actors and state-sponsored attacks, all the while educating students and professionals in cybersecurity.
Average Rating: 5 Stars
1 Reviews
Mohammad Turki A.
January 15, 2022
Yes, it does.
Combine technology training for employees with industry experts, mentors, and projects, for critical thinking that pushes innovation. Our proven upskilling system goes after success—relentlessly.
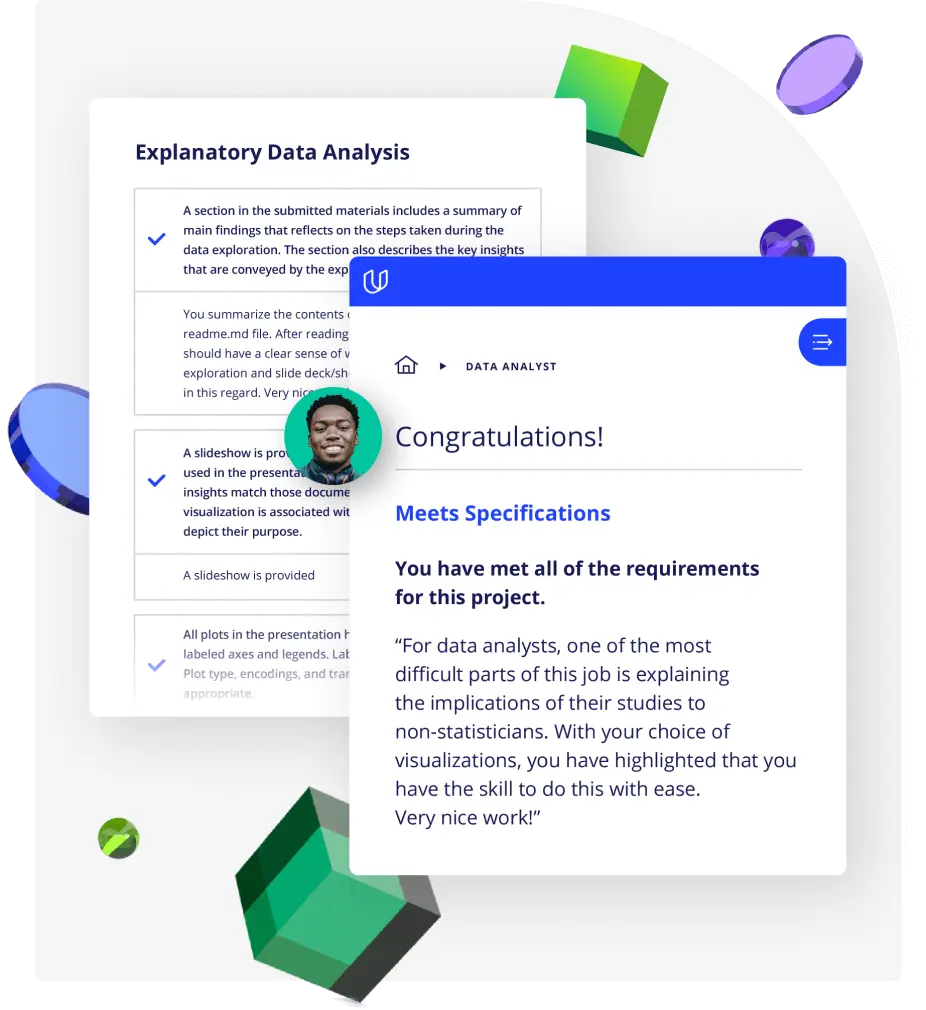
Demonstrate proficiency with practical projects
Projects are based on real-world scenarios and challenges, allowing you to apply the skills you learn to practical situations, while giving you real hands-on experience.
Gain proven experience
Retain knowledge longer
Apply new skills immediately
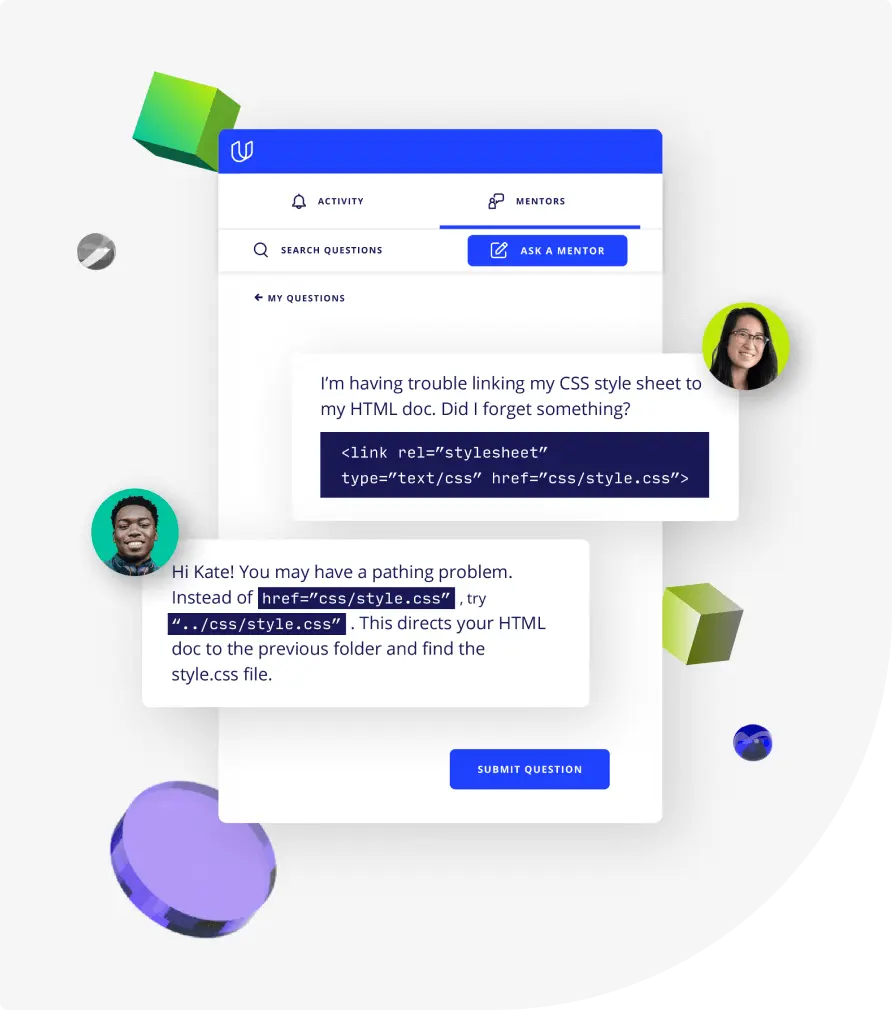
Top-tier services to ensure learner success
Reviewers provide timely and constructive feedback on your project submissions, highlighting areas of improvement and offering practical tips to enhance your work.
Get help from subject matter experts
Learn industry best practices
Gain valuable insights and improve your skills
Unlimited access to our top-rated courses
Real-world projects
Personalized project reviews
Program certificates
Proven career outcomes
Full Catalog Access
One subscription opens up this course and our entire catalog of projects and skills.
Average time to complete a Nanodegree program
(9)
4 months
, Intermediate
(32)
4 months
, Intermediate
4 weeks
, Beginner
4 weeks
, Beginner
(27)
4 months
, Intermediate
(115)
3 months
, Beginner
4 weeks
, Beginner
4 weeks
, Intermediate
(17)
2 months
, Advanced
4 weeks
, Beginner
(6)
4 weeks
, Beginner
4 weeks
, Intermediate
(269)
3 months
, Intermediate
(85)
3 months
, Intermediate
4 weeks
, Intermediate
4 weeks
, Intermediate

Enterprise Security
(9)
4 months
, Intermediate
(32)
4 months
, Intermediate
4 weeks
, Beginner
4 weeks
, Beginner
(27)
4 months
, Intermediate
(115)
3 months
, Beginner
4 weeks
, Beginner
4 weeks
, Intermediate
(17)
2 months
, Advanced
4 weeks
, Beginner
(6)
4 weeks
, Beginner
4 weeks
, Intermediate
(269)
3 months
, Intermediate
(85)
3 months
, Intermediate
4 weeks
, Intermediate
4 weeks
, Intermediate
Udacity's Java Web Developer Nanodegree program is tailored for those seeking to master Java in web development. This program, ideal for intermediate learners, teaches Java's role in creating robust server-side applications. You'll learn about technologies like Spring Boot, GraphQL, and Docker, gaining hands-on experience through practical projects. This Java developer program is structured to enhance your skills in Java for real-world application, preparing you for a successful career in software development. Our experienced instructors guide you through each module, ensuring a thorough understanding of Java's applications in modern web development. Completing this program equips you with a portfolio of projects, demonstrating your readiness for professional roles in the tech industry.