Lesson 1
Applied Cryptography
Course
Cryptography is present in everyday life, from paying with a credit card to using the telephone. Learn all about making and breaking puzzles in computing.
Cryptography is present in everyday life, from paying with a credit card to using the telephone. Learn all about making and breaking puzzles in computing.
Last Updated March 7, 2022
No experience required
Course Lessons
Lesson 2
Problem Set 1
Lesson 3
Q & A Session 1
Lesson 4
Lesson 2
Lesson 5
Problem Set 2
Lesson 6
Q & A Session 2
Lesson 7
Lesson 3
Lesson 8
Problem Set 3
Lesson 9
Q & A Session 3
Lesson 10
Lesson 4
Lesson 11
Problem Set 4
Lesson 12
Lesson 5
Lesson 13
Problem Set 5
Lesson 14
Lesson 6
Lesson 15
Problem Set 6
Lesson 16
Problem Set 6 Solutions
Lesson 17
Lesson 7
Lesson 18
Interview on GSM Cracking
Lesson 19
Final Assessment
Taught By The Best

Dave Evans
Instructor
The Udacity Difference
Combine technology training for employees with industry experts, mentors, and projects, for critical thinking that pushes innovation. Our proven upskilling system goes after success—relentlessly.
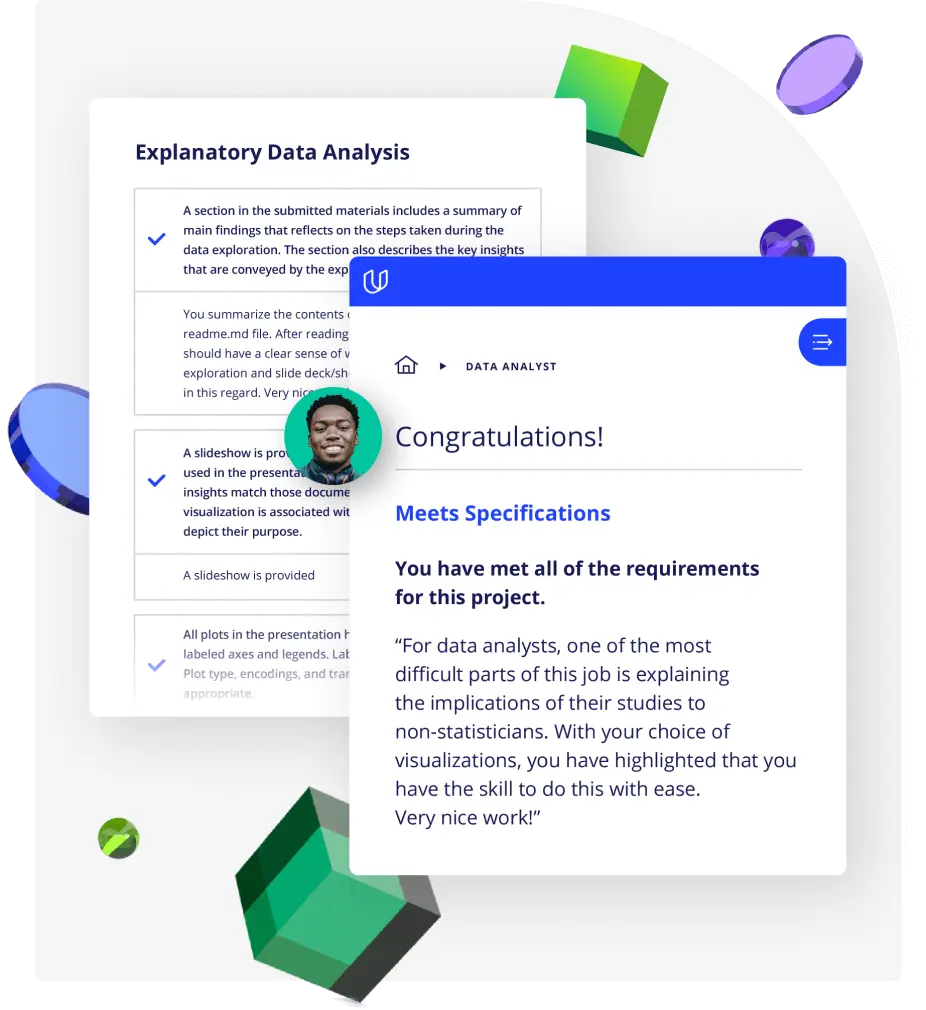
Demonstrate proficiency with practical projects
Projects are based on real-world scenarios and challenges, allowing you to apply the skills you learn to practical situations, while giving you real hands-on experience.
Gain proven experience
Retain knowledge longer
Apply new skills immediately
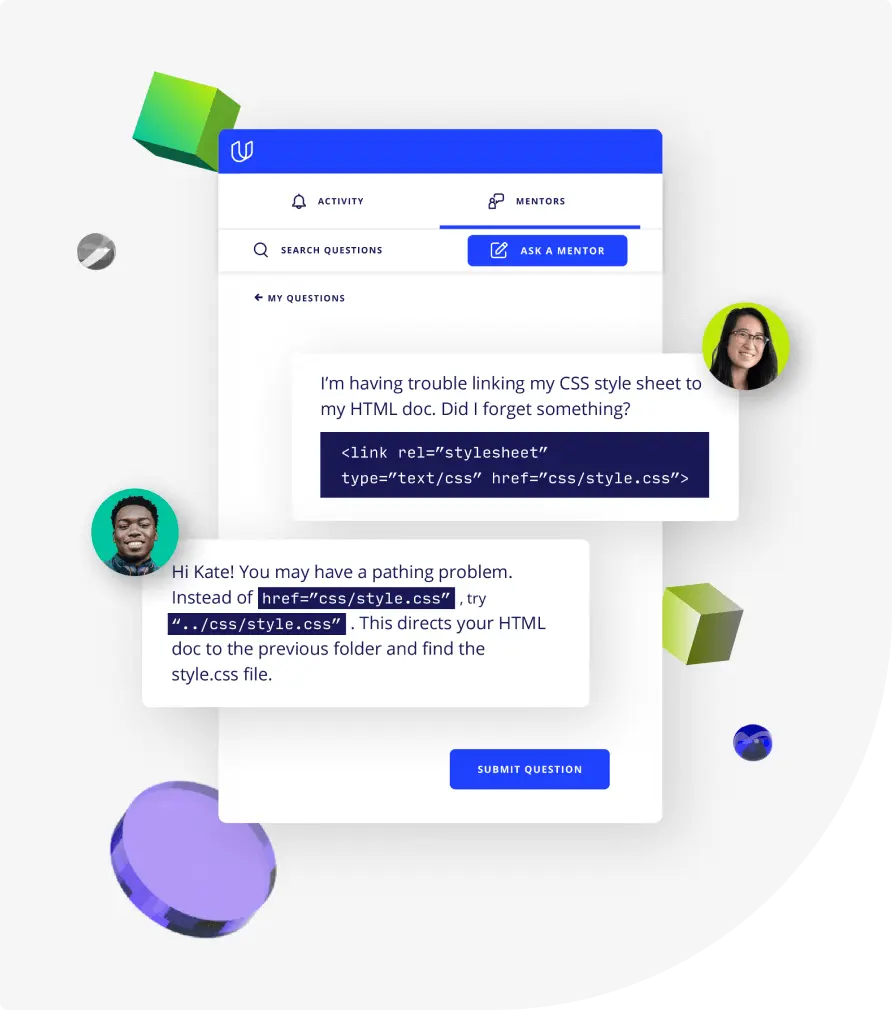
Top-tier services to ensure learner success
Reviewers provide timely and constructive feedback on your project submissions, highlighting areas of improvement and offering practical tips to enhance your work.
Get help from subject matter experts
Learn industry best practices
Gain valuable insights and improve your skills